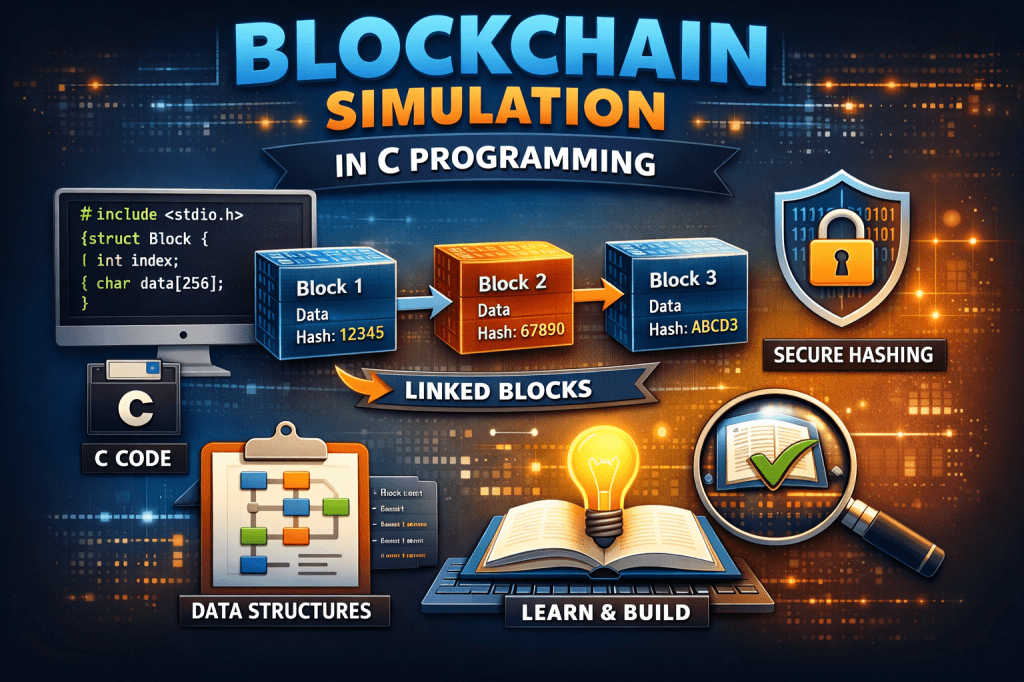
A complete educational walkthrough: from basic theory to a working blockchain written in the C programming language.
1. Why This Project Matters
If you truly want to understand how blockchain works, the best way is not watching videos or reading whitepapers — it is building one yourself.
When you write a blockchain in C, something powerful happens:
You stop thinking of blockchain as “crypto magic” and start seeing it as:
• Data structures
• Cryptography
• Hash functions
• Linked lists
• Memory management
• Time stamps
• Verification logic
In other words — it becomes Computer Science.
This tutorial does NOT implement a cryptocurrency like Bitcoin. Instead, we simulate the core mechanism that makes blockchain trustworthy: immutable chained blocks secured by hashing.
By the end, you will understand:
• Why blocks cannot be modified
• What mining actually is
• Why hashes matter
• How tampering is detected
• How consensus begins conceptually
And you will have a working blockchain program.
2. What Is a Blockchain (In Simple Words)
A blockchain is simply:
A linked list where each node contains the hash of the previous node.
That single idea is the entire invention.
Because if block 2 stores the hash of block 1…
And block 3 stores the hash of block 2…
Then changing any data breaks the entire chain after it.
This property is called:
Immutability
3. How a Block Looks Internally
Every block contains 5 important things:
- Index (block number)
- Timestamp
- Data (transaction/message)
- Previous Hash
- Current Hash
So conceptually:
Block = (Data + Previous Hash) → Hashed → Current Hash
4. Why C Language Is Perfect For This
Most tutorials use Python. That hides important details.
C forces you to learn:
• Memory layout
• Pointers
• Structs
• Manual linking of blocks
• String handling
Which means you will understand blockchain at the hardware‑level thinking layer.
5. Required Libraries
We will use:
stdio.hstdlib.hstring.htime.hstdint.hWe will also implement our own hash function (educational hash, not secure SHA‑256). Real blockchains use SHA‑256 but implementing it fully is very long and distracts from learning the structure.
6. Designing the Block Structure
In C, a block becomes a struct.
typedef struct Block { int index; long timestamp; char data[256]; unsigned int previousHash; unsigned int hash; struct Block* next;} Block;Explanation
index → position in chain
timestamp → when block created
data → transaction information
previousHash → hash of previous block
hash → current block hash
next → pointer to next block (linked list)
You just created the foundation of a blockchain.
7. Understanding Hashing
A hash function converts any input into a fixed‑size number.
Example:
“Hello” → 439329280
“Hello!” → 12939102
Even a tiny change produces a completely different hash.
This is called the Avalanche Effect.
We now write a simple hash function.
unsigned int calculateHash(int index, long timestamp, char *data, unsigned int previousHash) { unsigned int hash = 0; hash = index; hash ^= timestamp; for(int i = 0; data[i] != '\0'; i++) hash = hash * 31 + data[i]; hash ^= previousHash; return hash;}What This Does
• Combines all block fields
• Produces a number
• Any modification changes output
This number protects the block.
8. Creating the Genesis Block
The first block in a blockchain is special.
It is called the Genesis Block.
It has no previous block.
So previousHash = 0
Block* createGenesisBlock() { Block* block = (Block*)malloc(sizeof(Block)); block->index = 0; block->timestamp = time(NULL); strcpy(block->data, "Genesis Block"); block->previousHash = 0; block->hash = calculateHash(block->index, block->timestamp, block->data, block->previousHash); block->next = NULL; return block;}Now your blockchain has a starting point.
9. Adding New Blocks
Every new block uses the previous block’s hash.
Block* createBlock(Block* previous, char *data) { Block* newBlock = (Block*)malloc(sizeof(Block)); newBlock->index = previous->index + 1; newBlock->timestamp = time(NULL); strcpy(newBlock->data, data); newBlock->previousHash = previous->hash; newBlock->hash = calculateHash(newBlock->index, newBlock->timestamp, newBlock->data, newBlock->previousHash); newBlock->next = NULL; previous->next = newBlock; return newBlock;}Now we have a chain.
10. Printing the Blockchain
void printChain(Block* head) { Block* current = head; while(current != NULL) { printf("\nBlock %d", current->index); printf("\nTimestamp: %ld", current->timestamp); printf("\nData: %s", current->data); printf("\nPrevious Hash: %u", current->previousHash); printf("\nHash: %u\n", current->hash); current = current->next; }}11. Verifying the Chain (The Magic Part)
This is what makes blockchain powerful.
We check:
- Does each block’s stored hash match a recalculated hash?
- Does each block correctly reference the previous block?
int isChainValid(Block* head) { Block* current = head; while(current->next != NULL) { if(current->hash != calculateHash(current->index, current->timestamp, current->data, current->previousHash)) return 0; if(current->next->previousHash != current->hash) return 0; current = current->next; } return 1;}If anyone edits a block — validation fails instantly.
12. Main Function
int main() { Block* blockchain = createGenesisBlock(); createBlock(blockchain, "Alice pays Bob 10 coins"); createBlock(blockchain->next, "Bob pays Charlie 5 coins"); createBlock(blockchain->next->next, "Charlie pays David 2 coins"); printChain(blockchain); if(isChainValid(blockchain)) printf("\nBlockchain is VALID\n"); else printf("\nBlockchain is TAMPERED\n");}Compile:
gcc blockchain.c -o blockchain./blockchain13. Try Breaking It (Important Experiment)
Open memory and change:
strcpy(blockchain->next->data, "Alice pays Bob 1000 coins");Run validation again.
The blockchain becomes INVALID.
That is exactly how real blockchain detects fraud.
14. What We Did NOT Implement (Real Blockchain Features)
Real systems also include:
• SHA‑256 cryptography
• Proof‑of‑Work mining
• Nonce values
• Peer‑to‑peer networking
• Distributed consensus
• Wallet signatures (public/private keys)
But now — those are understandable.
15. What You Just Learned (Very Important)
You learned that blockchain is NOT magic.
It is the combination of:
Linked List + Hashing + Verification Logic + Time Ordering
That’s it.
And this is why companies value developers who understand low‑level implementation — because they understand systems, not just libraries.
16. Next Challenges (Highly Recommended)
Try extending this project:
- Add a nonce and mining difficulty
- Implement proof‑of‑work
- Add file storage inside blocks
- Save the chain to disk
- Load blockchain from file
- Implement digital signatures
- Implement networking between two programs
If you can do those — you will truly understand blockchain technology, not just use it.
Leave a comment